Nothing is more powerful than a community determined to defend against hacks, scams, and fraudulent activities. Together we will overcome the decentralization disparity and turn it into advantage for security.
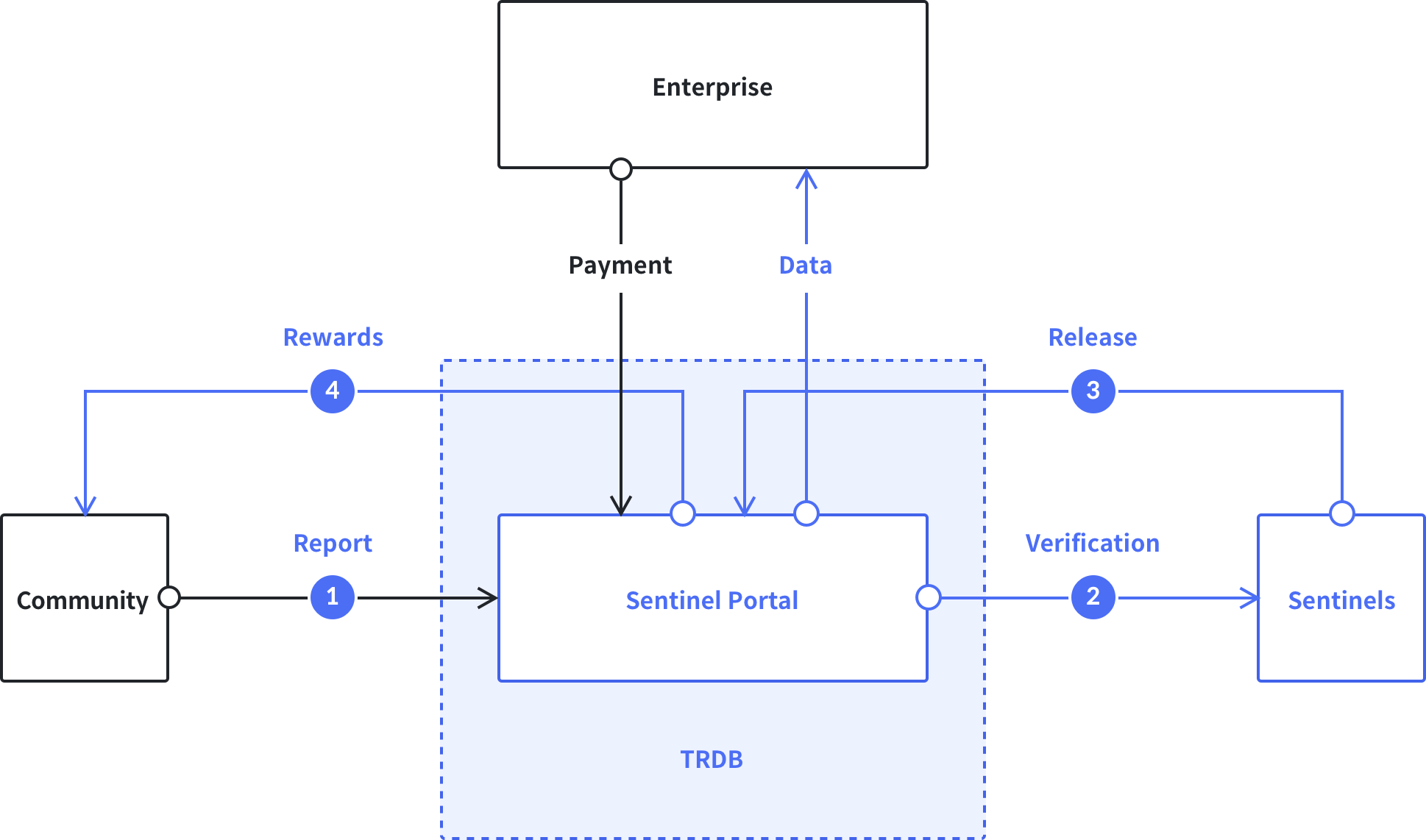
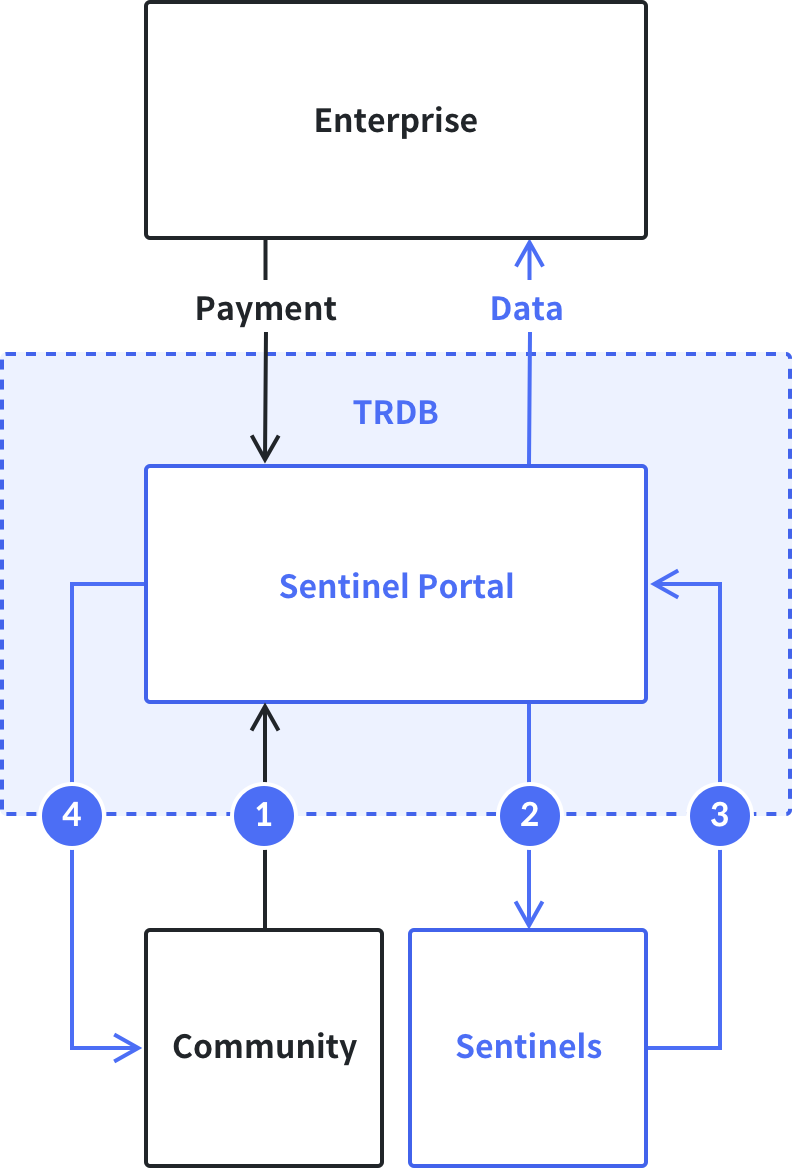
Report
Users can report suspicious cyber incidents including malware, hacks, phishing scams, and fraud.
Verification
All reported data from the Sentinel Portal would be reviewed and validated by our security experts, also known as the Sentinels.
Release
The validated data would be published onto the blockchain via the TRDB so users get real-time access to crowdsourced information on the latest security threats.
Rewards
Rewards for valuable contributions by reporting threat intelligence data.